Cyberspace enables and shapes the modern world - a complex system of systems with connective threads, unconstrained by borders or geography. It permeates civil and military sectors and is difficult to regulate, control or to impose national authority on.
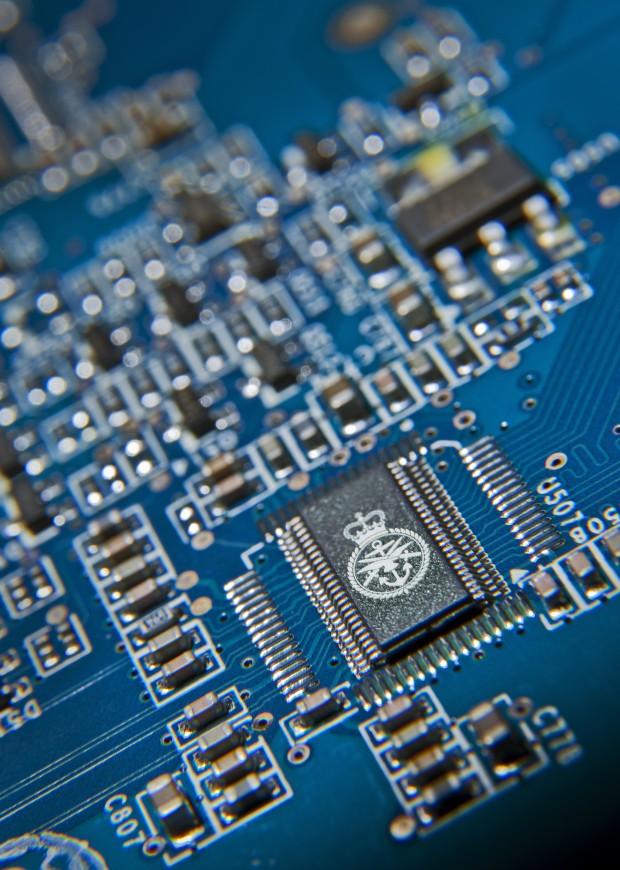
The MOD cyber research programme in partnership with other government departments, aims to develop and apply advances in cyber security science and technology to protect and react to attacks against its digital assets or freedom to operate in cyberspace. Plans include activities to support defence needs, including the UK’s ability to detect and defend itself against cyber attack from terrorists, states, or other hostile actors.
It also addresses shortcomings in the critical cyber infrastructure aimed at tackling immediate weaknesses in security and ensuring that the UK maintains access to a trusted industrial base. There is also the need to create and retain talent within the sector and promote a wider understanding of cyber across defence.

MOD is developing innovative approaches and solutions to identify risks in civil and military systems, technologies, processes and methods which could influence or degrade system operations and find ways that these can be countered. This covers systems connected to the Internet and those accessible (open) or disconnected and isolated (closed) to other networks.
One of the key potential threats to digital assets is the abuse of legitimate credentials, either by individuals or malware. As cyberspace evolves and expands, the insider threat is expected to continue to grow with potentially severe operational impact on defence, such as a loss of confidentiality, integrity and availability of information and supporting system services and resources.
Current R&D is investigating the detection of cyber insider threats using a host-based solution - end user client devices, including those deployed on platforms such as vehicles, ships and aircraft including their device memory, configuration, audit and logs. Technical developments include ensuring the denial of access to areas, carrying out unauthorised alteration of logs or audit traces, running unauthorised programmes or scripts, the unauthorised copying or transferring of files or data, or activating or changing parameters of real- time operating systems. Innovative solutions are also being developed to detect and characterise anomalous and abnormal behaviour. These include application of social and behavioural sciences to characterise the threats and identify behavioural and sociotechnical indicators.
This is an exciting area to be working in with other government departments, aimed at providing an improved understanding of cyberspace, enhancing the UK’s military capabilities and protecting the UK’s vital computer network and facilities.
MOD is seeking proposals for an automated cyber defence response which will include collecting information, identifying the attack, analysing potential courses of action and then responding. The Centre for Defence Enterprise themed competition is looking for proof-of-concept research proposals for tools and techniques that support the planning and carrying out of responses to threats to our systems. The competition closes on Thursday 23 October 2014.